Your global IP address is 63.239.94.10 while your local one is 10.71.2.195. You are behind a NAT. Your local address is in unroutable address space.
Your machine numbers TCP source ports sequentially. The following graph shows connection attempts on the X-axis and their corresponding source ports used by your computer on the Y-axis.
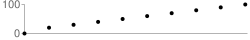
TCP ports are not renumbered by the network.
- en0: (an ethernet interface)
- fe80::60c:ceff:fedb:8222 [mnot-laptop.local] (a link-local IPv6 address)
- 10.71.2.195 (a private IPv4 address)
- lo0: (a local loopback interface)
- ::1 [localhost] (an IPv6 loopback address)
- fe80::1 (a link-local IPv6 address)
- 127.0.0.1 [localhost] (an IPv4 loopback address)
- utun0:
- 172.19.124.56 (a private IPv4 address)
A DNS proxy or firewall generated a new request rather than passing the client's request unmodified.
A DNS proxy or firewall caused the client's direct DNS request to arrive from another IP address. Instead of your IP address, the request came from 74.125.187.209.
We are unable to deliver non-DNS UDP datagrams to our servers. Possible reasons include a restrictive Java security policy, a blocking rule imposed by your firewall or personal firewall configuration, or filtering performed by your ISP. Although it means we cannot conduct the latency and bandwidth tests, it does not necessarily indicate a problem with your network.
Netalyzr detected the following proxies:
- Port: 80 (HTTP), Response Time: 29 ms
Changes to headers or contents sent between the client and our HTTP server show the presence of an otherwise unadvertised HTTP proxy.
The following headers had their capitalization modified by the proxy:
- Content-Type: text/html
- Content-Length: 698
- Last-Modified: Tue
- 18 Jun 2013 06:19:19 GMT
- Set-Cookie: netAlizEd=BaR; path=/; domain=netalyzr.icsi.berkeley.edu
- Connection: keep-alive
The following headers were added by the proxy to HTTP responses:
- Via: [1.1 localhost:3128 (squid/2.7.STABLE3)]
- X-Cache-Lookup: [MISS from localhost:3128]
- X-Cache: [MISS from localhost]
- Proxy-Connection: keep-alive
The detected proxy reordered the headers sent from the server.
The detected HTTP proxy changed either the headers the client sent or the HTTP response from the server. We have captured the changes for further analysis.
The detected HTTP proxy may cause your traffic to be vulnerable to CERT Vulnerability Note 435052. An attacker might be able to use this vulnerability to attack your web browser.
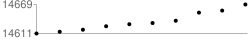
Your ISP's DNS resolver does not randomize its local port number. This means your ISP's DNS resolver is probably vulnerable to DNS cache poisoning, which enables an attacker to intercept and modify effectively all communications of anyone using your ISP.
We suggest that, if possible, you immediately contact your network provider, as this represents a serious vulnerability.
The following graph shows DNS requests on the x-axis and the detected source ports on the y-axis.
| Name | IP Address | Reverse Name/SOA |
|---|---|---|
| www.bankofthewest.com | 204.44.12.103 | X |
| www.sterlingsavingsbank.com | 12.69.145.232 | X |
- User Agent: Java/1.6.0_45
- Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
- Accept Language: en-us,en;q=0.5
- Accept Encoding: gzip,deflate
- Accept Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7



